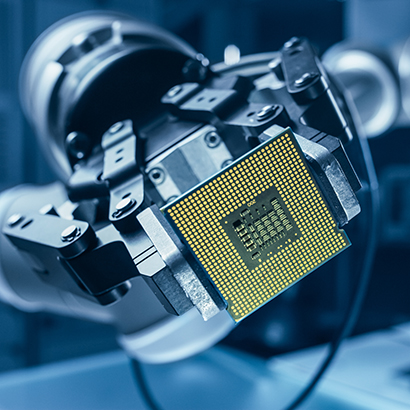
Manufacturing Technologies
New privacy regulations along with new sets of guidelines in relation to the principle of “privacy by design” require thorough implementation in a company’s terms and conditions, reporting, and elsewhere. A secure communication management framework, such as the e-ID concept, is needed to comply with EU regulatory requirements, for example.
As automation propels big data, we help our clients develop effective solutions for protecting and managing information assets and complying with data protection law, including the preparation of expert opinions regarding data protection issues, drafting data protection guidelines, assisting with the appointment of data protection supervisors, and settling data protection issues in connection with compliance investigations.
Cyber threats are a growing concern for manufacturers of all sizes. Most manufacturers are critical infrastructure organizations with automated processes, intellectual property, and other sensitive information that may be vulnerable to cyber attacks. We help manufacturers prevent and deter attacks, pursue perpetrators, and mitigate risk and loss. Our team includes members with extensive experience in public policy, cyberforensic investigations, Internet tracking, rapid response, and insurance coverage.
Thought Leadership
The Australian Federal Budget for 2026–2027 proposes far-reaching changes to the Australian tax system that will have significant impacts on a range of taxpayers.
The year 2025 saw significant regulatory activity in the realm of digital assets. The US Congress and financial regulators took steps to create and implement a clear legal framework to facilitate financial transactions using digital assets, and they will continue to do so in 2026.
Texas is home to 31.3 million people, and with two of the country’s leading metropolitan areas by economic output, Texas is the world’s eighth largest economy at US$2.7 trillion.
The Washington state legislature has adjourned for 2026, and key tax changes are in store if Governor Bob Ferguson signs several tax-related bills into law, and if those tax changes then survive expected legal challenges.

